Product Overview
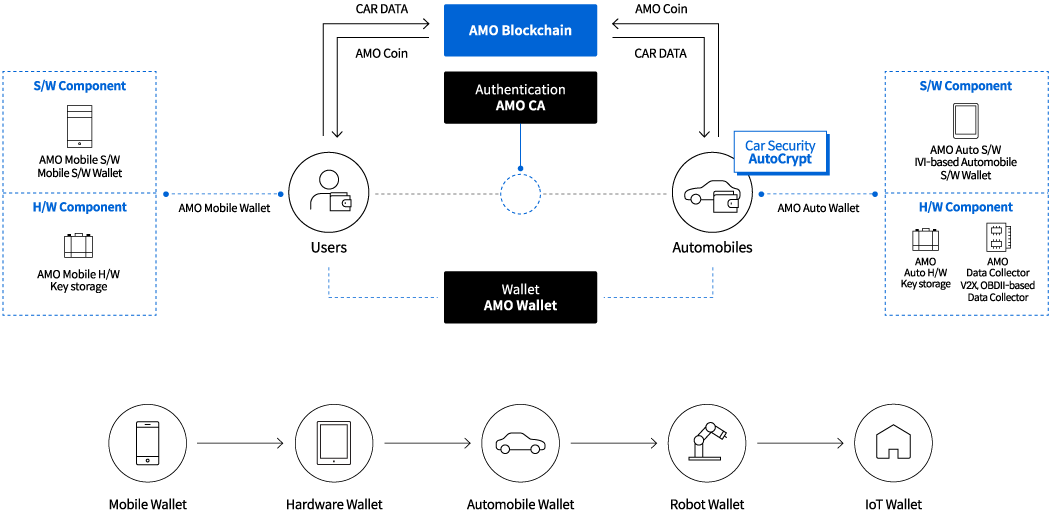
Car Data Collection requires a high level of technical expertise and experience from development to implementation. For sensitive or personalized data that may be collected, de-identification and encryption will be applied. For data-ownership and authorization, authentification, access control and encryption will be embedded during the process of system architectural design.
AMO WALLET S
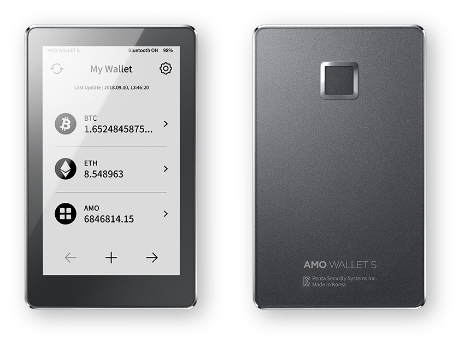
AMO Wallet S is a hardware cryptocurrency wallet that supports various cryptocurrencies. Its sophisticate touchscreen functionality, along with its cutting-edge biometric security provides the ultimate cryptocurrency storage system for your use. AMO Wallet S can be connected to AMO Wallet Mobile with Bluetooth.
AMO DATA Collector

AMO Data Collector effortlessly gathers all car data - velocity, mileage, repair, engine oil check-up/analysis, etc. - just by attaching the device to the car's OBD-II. All data is encrypted and safely stored. By connecting AMO Data Collector to one's smart phone, the data will be delivered to the blockchain network.
AMO CA
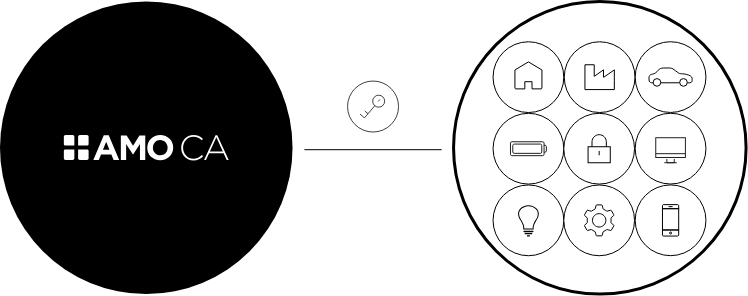
The IoT environment has various things connected by the internet, enabling convenient user experience. Subsequently, businesses in various industries are utilizing interconnected devices to increase business efficiency. However, concerns of privacy violation such as information regarding user location and access records continue to rise, and incidents of IoT devices being abused are incrementally surfacing. In order to decrease such risk factors, IoT devices must be safely authenticated and managed, data inside devices and in transit be encrypted, and message integrity be guaranteed.
 en
en